Using Forensic Artefacts for Penetration Testing
In my last post, OSCP as a Digital Forensics/Incident Response Analyst, I made the comment that DFIR and Penetration Testing skill sets are complimentary. The purpose of this post is for me to investigate how digital forensic knowledge can be practically applied to a penetration test or red team activity to identify valuable data and assist in remaining undetected.
Many of the artefacts discussed are not 'secret' or 'advanced' forensic artefacts. In fact, some of the artefacts discussed are incredibly common, such as Windows event logs. These artefacts, whilst common, are a record of user and system activity and can be used to reconstruct events on the system. Knowledge of these artefacts and the data they store can be valuable during forensic investigations.
All techniques detailed in this article are executed through native Windows Powershell, and do not rely on any third party forensic tools.
Many of the artefacts discussed are not 'secret' or 'advanced' forensic artefacts. In fact, some of the artefacts discussed are incredibly common, such as Windows event logs. These artefacts, whilst common, are a record of user and system activity and can be used to reconstruct events on the system. Knowledge of these artefacts and the data they store can be valuable during forensic investigations.
All techniques detailed in this article are executed through native Windows Powershell, and do not rely on any third party forensic tools.
It it worth noting that this post is about applying digital forensic knowledge to a penetration test. The actions performed will definitely modify the current state of the system.
What this post will not be:
Remote Desktop Logs for Credential Re-Use:
Understanding which computers have remotely logged in to your client PC can provide direction for credential re-use and pass the hash attacks on a corporate environment without the need for port scanning. Remote desktop is often restricted to administrative users, so identifying an IP address that has remotely connected to the client may identify a PC with administrative credentials.
Luckily for us, Windows logs an event for successful login attempts (Event 4624) with a logon type for remote desktop and terminal services (type 10). It even records the source IP within the message of the log.
To return all event log values from a successful RDP login to your client, use the following command:
Note: This command requires local administrator privileges.
To return only the source IP, account domain and account name:
Note: This command requires local administrator privileges.
Email/Document Index Search via WaitList.dat (touch screen devices only)
In a previous post, I analysed 'WaitList.dat'. WaitList.dat is a full text index data store of emails and documents on Windows touch screen tablets and laptops . This is very convenient artefact for a penetration tester, as it provides a central text based data store for string searches over emails and documents.
In order to search WaitList.dat, you will first need to kill the process 'SearchIndexer.exe' and wait a short time for the file to be released. There is no user notification when SearchIndexer is killed. To search for passwords, use the following Powershell command.
Note: This command requires local administrator privileges.
Recent Items
Identifying recent files and folders the user has opened will assist with three things:
From this list we may also look for programs with network access capability (e.g. SSH clients) as these will contain remote connection configurations which may be used for lateral movement.
Internal Web Server Identification Through Bookmarks/Favourites
Web browser bookmarks/favourites often contain links to internal webapps and web servers. Some companies are less stringent with patching internal web apps, which make them a valuable target for a penetration tester.
The following Powershell one liners parse the current user's bookmarks/favourites from different popular browsers:
Internet Explorer Favorites:
Chrome Bookmarks:
Firefox Bookmarks:
Firefox uses an SQLite database to store bookmarks. SQLite libraries are available for Powershell, however they are not native. If you need to extract these values you may need to use third party scripts.
Edge Bookmarks:
Edge uses an Extensible Storage Engine (ESE) database to store bookmarks. If you need to extract these values you may need to use third party scripts/programs.
What this post will not be:
- A guide on how to clean up forensic artefacts post exploitation.
- A complete list of all forensic artefacts that will be useful to a penetration tester.
Scenario
In order to investigate this idea, let's imagine the following scenario. You have scraped a number of client email addresses from social media, sent some Microsoft Word client side exploits over email and a user has opened the document, providing you with a reverse shell to their system.
Approach
From a forensics perspective, it is important to limit non-essential interaction with the client. The following examples are some actions which will create evidence on disk and in memory, leaving them at the mercy of anti-virus, endpoint detection/response and blue team.
- Dropping files
- Modifying files
- Executing programs
- Network usage
- More...
Limiting the frequency of these actions, and using native/pre-installed software known to be used by your current user (more on this below) can assist in remaining undetected whilst the achieving the penetration test objective.
Enumeration
Once a shell is obtained, a penetration tester will enumerate the system and identify options for persistence and lateral movement. Lets take a look at ways in which forensic artefact knowledge can assist in this process.Remote Desktop Logs for Credential Re-Use:
Understanding which computers have remotely logged in to your client PC can provide direction for credential re-use and pass the hash attacks on a corporate environment without the need for port scanning. Remote desktop is often restricted to administrative users, so identifying an IP address that has remotely connected to the client may identify a PC with administrative credentials.
Luckily for us, Windows logs an event for successful login attempts (Event 4624) with a logon type for remote desktop and terminal services (type 10). It even records the source IP within the message of the log.
To return all event log values from a successful RDP login to your client, use the following command:
Note: This command requires local administrator privileges.
Get-EventLog -Log Security | where {$_.eventID -eq 4624 -and $_.message –match "Logon Type:\s*10”} | Format-List -Property *
To return only the source IP, account domain and account name:
Note: This command requires local administrator privileges.
Get-EventLog -Log Security | where {$_.eventID -eq 4624 -and $_.message –match "Logon Type:\s*10”} | Select -expand Message | ForEach-Object {[regex]::Match($_, 'Source Network Address:\s(.*)\s*').Groups[1].Value;[regex]::Match($_, 'Account Domain:\s(.*)\s*').Groups[1].Value, [regex]::Matches($_, 'Account Name:\s(.*)\s*').Groups[1].Value}
Email/Document Index Search via WaitList.dat (touch screen devices only)
In a previous post, I analysed 'WaitList.dat'. WaitList.dat is a full text index data store of emails and documents on Windows touch screen tablets and laptops . This is very convenient artefact for a penetration tester, as it provides a central text based data store for string searches over emails and documents.
In order to search WaitList.dat, you will first need to kill the process 'SearchIndexer.exe' and wait a short time for the file to be released. There is no user notification when SearchIndexer is killed. To search for passwords, use the following Powershell command.
Note: This command requires local administrator privileges.
Stop-Process -name "SearchIndexer" -force;Start-Sleep -m 500;Select-String -Path $env:USERPROFILE\AppData\Local\Microsoft\InputPersonalization\TextHarvester\WaitList.dat -Encoding unicode -Pattern "password"
Recent Items
Identifying recent files and folders the user has opened will assist with three things:
- Profiling the business role of your current user.
- Identify recent documents and business processes. These can be leveraged for social engineering, or even contain passwords (if you are lucky).
- Identify contextual files on remote network shares and external hard drives - even if those shares/drives are no longer connected.
A common source of recent item access is the 'Recent Items' directory, located in the 'C:\Users\%USER%\AppData\Roaming\Microsoft\Windows\Recent' directory. This directory contains contains shortcut files (.lnk) to files and folders recently accessed by the current user. The creation date on a lnk file indicates the first time a file by this name was opened by the user, and the modification date indicates the last time a file by this name has been opened by the user.
To obtain a listing of recent item *.lnk files and their associated creation and modification times, you can use this Powershell one liner:
Get-ChildItem $env:USERPROFILE\AppData\Roaming\Microsoft\Windows\Recent\ -recurse -include @("*.lnk") | Select-Object Name, CreationTime, LastWriteTime | sort LastWriteTime -Descending
In order to parse the actual file location from the *.lnk file (even if it exists/existed on a network share or USB drive) use this Powershell 'one liner':
$sh = New-Object -ComObject WScript.Shell;Get-ChildItem $env:USERPROFILE\AppData\Roaming\Microsoft\Windows\Recent -Filter *.lnk | ForEach-Object {$sh.CreateShortcut($env:USERPROFILE+'\AppData\Roaming\Microsoft\Windows\Recent\'+$_).TargetPath}
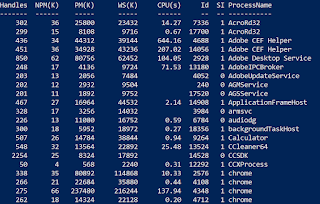
Program Execution
Program execution artefacts can inform a penetration tester of programs which have previously been executed on a system. Utilising tools which are regularly executed on the system can assist in evading AV software that perform user behaviour analysis.
One common source of program execution evidence are prefetch files. Prefetch files are created when an executable by that name is first executed, and are modified each time an executable program by that name is executed.
Note: This command requires local administrator privileges.
Get-ChildItem C:\Windows\Prefetch -recurse -include @("*.pf") | Select-Object Name, CreationTime, LastWriteTime | sort LastWriteTime -Descending
From this list we may also look for programs with network access capability (e.g. SSH clients) as these will contain remote connection configurations which may be used for lateral movement.
Internal Web Server Identification Through Bookmarks/Favourites
Web browser bookmarks/favourites often contain links to internal webapps and web servers. Some companies are less stringent with patching internal web apps, which make them a valuable target for a penetration tester.
The following Powershell one liners parse the current user's bookmarks/favourites from different popular browsers:
Internet Explorer Favorites:
Get-ChildItem ([Environment]::GetFolderPath('Favorites')) -File -Recurse | ForEach {[pscustomobject]@{Name = $_.Name; URL = ($_ | Select-String "^URL").Line.Trim("URL=")}}
Chrome Bookmarks:
Get-Content "$Env:USERPROFILE\AppData\Local\Google\Chrome\User Data\Default\Bookmarks" | out-string | ConvertFrom-Json | ForEach-Object {$_.roots.bookmark_bar.children | Select Name,URL}
Firefox Bookmarks:
Firefox uses an SQLite database to store bookmarks. SQLite libraries are available for Powershell, however they are not native. If you need to extract these values you may need to use third party scripts.
Edge Bookmarks:
Edge uses an Extensible Storage Engine (ESE) database to store bookmarks. If you need to extract these values you may need to use third party scripts/programs.
Conclusion
In this post I have provided five examples which demonstrate how forensic knowledge can be applied to an offensive penetration testing or red team engagement. Whilst these techniques may not become a core process in your penetration testing methodology, they do demonstrate how different schools of knowledge, such as DFIR and Penetration Testing, can be complimentary.


This comment has been removed by a blog administrator.
ReplyDeleteThis comment has been removed by a blog administrator.
ReplyDeleteThank you for your articles that you have shared with us. Hopefully you can give the article a good benefit to us. Fundamentos de Microsoft Teams para negocios
ReplyDeleteLucky Club Casino Site - Find the Best Games and Bonuses
ReplyDeleteLucky luckyclub.live Club Casino Review 2021. Lucky Club Casino is one of the top online gambling sites in the world. It offers hundreds of games and has
Passover is a time for joy and tradition! Share the spirit with beautiful greetings from this helpful guide on how to wish Happy Pesach.
ReplyDeleteHm
ReplyDeleteLovingEcards’ Office Cards make it easy to send thank you employee ecards across teams. Pick from professional or fun designs, personalize with heartfelt messages, and share instantly to recognize your team’s efforts and show your appreciation in the workplace.
ReplyDeleteThe **printable-style thank you eCards ** from LovingEcards are simply wonderful! Each card beautifully blends creativity and elegance, allowing you to express heartfelt gratitude in style. I love how easy they are to customize and share instantly. Whether printed or sent digitally, these eCards make saying “thank you” more personal and memorable.
ReplyDeleteI found Farewell Farewell MessagesMessages to be incredibly helpful for writing meaningful farewell cards. Whether you’re making a farewell card for coworker, designing group leaving cards, or creating a goodbye card, these ideas make your message truly unforgettable.
ReplyDeleteUsing forensic artefacts for penetration testing is a smart approach, as it bridges the gap between incident response and proactive security assessment. This topic clearly explains how analysing logs, memory dumps, and system traces can strengthen vulnerability detection and improve defensive strategies. Such practical insights are valuable for students working on technical or interdisciplinary assignments. For those managing heavy academic workloads in healthcare studies as well, support services like nursing assignment help brisbane can provide useful academic assistance alongside demanding coursework.
ReplyDeletecomprar carta
ReplyDeleteComprar carta online
fuhrerschein kaufen
rijbewijs kopen online
mpu gutachten kaufen
Kopa kokot
Comprar patente
rijbewijs kopen online
koupit ridicsky prukaz online
acheter permis de conduire en France